New leak analyses mapped Claude Code's hook system, compaction behavior, and background-agent scaffolding, and community researchers said the cch signing scheme is now fully reverse engineered. The details turn an npm source-map exposure into concrete notes on agent guardrails, session handling, and third-party compatibility.
cch= request-signing system is now fully mapped, after earlier posts flagged that Anthropic was computing a hash below the JavaScript layer and attaching it to API traffic Early cch signing warning Reverse engineering claim.PreToolUse, PermissionRequest, PermissionDenied, PreCompact, and PostCompact (Alex Kim's analysis, Claude Code Unpacked, Hooks reference, HN summary of leak findings).You can read the source leak write-up, browse the interactive Claude Code Unpacked, and compare those findings to Anthropic's own hooks reference and settings docs. The interesting bit is how much of the runtime shape is now visible: decoy tools, compaction failure counters, hook events that line up with official docs, and a client attestation scheme that the reverse-engineering crowd says they have already cracked Reverse engineering claim.
The clearest new technical thread after the initial leak was cch=. Alex Kim's read of the leaked code says Claude Code places a cch=00000 placeholder into a billing header, then Bun's native HTTP stack replaces those zeros with a computed hash before the request leaves the process, letting Anthropic validate that traffic came from a genuine Claude Code client rather than a lookalike Alex Kim's analysis.
That is the same mechanism Paolo Anzani first warned about, and later said had been fully reverse engineered by community researchers Early cch signing warning Reverse engineering claim. The public evidence here is stronger on existence than on robustness: the signing path appears real, but the only fresh claim about the bypass is the researchers' statement that they cracked it.
The Claude Code Source Leak: fake tools, frustration regexes, undercover mode
1.4k upvotes · 570 comments
The leak mattered because it exposed the agent's control plane, not just its prompt text. Community analysis and the official docs now line up on the same core lifecycle surface:
PreToolUse, before a tool call, can block executionPermissionRequest, when Claude Code raises a permission dialogPermissionDenied, after the auto mode classifier rejects a toolPostToolUse and PostToolUseFailure, after executionPreCompact and PostCompact, around context compactionSessionStart, SessionEnd, SubagentStart, and SubagentStop, around longer-running session and agent activityHooks reference documents those events directly. Claude Code settings also says project settings can be shared for permissions, hooks, and MCP servers, which fits the leak-era discussion that the hook system was clean enough to build tooling on top of Fresh HN discussion on hooks.
Claude Code Unpacked : A visual guide
1.1k upvotes · 397 comments
The most useful leak detail for people building long-running agents was the context stack. One widely shared summary broke it into four layers: HISTORY_SNIP, Microcompact, CONTEXT_COLLAPSE, and Autocompact Zhihu thread roundup.
Alex Kim's post adds the ugly production number attached to that system: a code comment saying repeated autocompact failures were wasting roughly 250,000 API calls a day globally before a MAX_CONSECUTIVE_AUTOCOMPACT_FAILURES = 3 cap was added Alex Kim's analysis. HN follow-up discussion around Claude Code Unpacked tied the same subsystem to conservative rereads, permission interruptions, and fragile session resume once contexts get long Fresh HN discussion on Unpacked.
Claude Code Unpacked : A visual guide
1.1k upvotes · 397 comments
The most bookmark-worthy roadmap leak was KAIROS. Across blog analysis, the interactive code map, and HN discussion, it shows up as scaffolding for an always-on agent with daily logs, GitHub webhook subscriptions, background daemon workers, and scheduled refreshes every five minutes (Alex Kim's analysis, Claude Code Unpacked).
That is distinct from the normal request-response CLI shape. Fresh HN comments highlighted a reported 15-second blocking budget and described KAIROS as a materially different interruption-aware background mode, while the same Unpacked project also surfaced adjacent unreleased pieces like Bridge remote control and Daemon Mode Fresh HN discussion on hooks HN on Claude Code Unpacked.
Fresh discussion on The Claude Code Source Leak: fake tools, frustration regexes, undercover mode
1.4k upvotes · 570 comments
Fresh discussion on Claude Code Unpacked : A visual guide
1.1k upvotes · 397 comments
CAREFUL: anthropic built a signature system into claude code. every API request gets signed with a cch= hash thats computed in compiled zig code if you recompile the client yourself it just sends zeros instead. they can instantly tell its not legit right now you literally can't Show more
we cracked it. the cch= signing system in claude code is fully reverse engineered - all credits for the work go to @ssslomp who did an amazing re work now any opensource client can let users actually use the anthropic subscription they already paid for. with whatever tool they Show more
CAREFUL: anthropic built a signature system into claude code. every API request gets signed with a cch= hash thats computed in compiled zig code if you recompile the client yourself it just sends zeros instead. they can instantly tell its not legit right now you literally can't
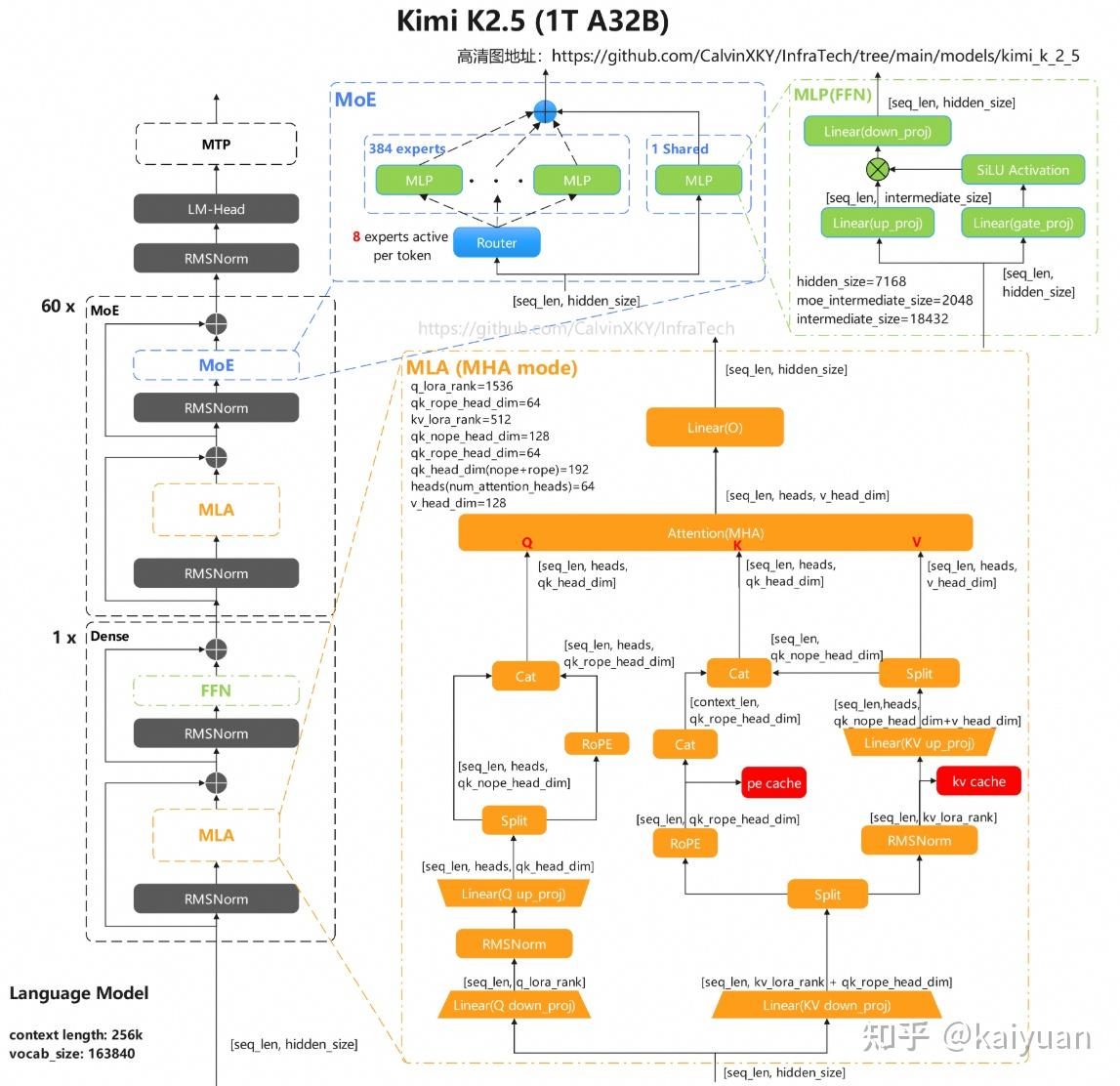
🔥 What makes Kimi K2.5 a standout in 2026’s multimodal AI race? Here’s a deep dive into its core architecture from Zhihu contributor kaiyuan 👇 🤖 Core Foundation (Vision-Language Native Design) • Built on Kimi-K2-Base, pre-trained on ~15T mixed vision & text tokens 📊 • Show more
🧵As 2026 unfolds, sparse MoE models are emerging as the new backbone for high-throughput inference and Agent workloads. Step 3.5 Flash from StepFun @StepFun_ai stands out with its efficient attention mixture design. Here’s a technical deep dive from Zhihu contributor kaiyuan 👇
Best post on the Claude Code source code leak. Most interesting bit: 'KAIROS' > the always on, proactive agent Anthropic plans to release.