Builder posts shared a GCP key scanner after the Gemini API-key incident, plus a lightweight gateway for per-user usage tracking and config-routed model abstractions with fallbacks. Use the audits and routing layers to limit misuse, but note OpenClaw still flags some API-calling skills and local scripts as suspicious.
generativelanguage.googleapis.com is enabled on each GCP project and flags both unrestricted keys and keys explicitly allowed to call Gemini.You can dig through the original HN discussion, browse the keyguard repo, and compare it with the dnc-ai-gateway repo. The useful bit is how quickly builders converged on the same control stack, audit the keys you already have, route requests through one choke point, and keep model choice in config instead of app code.
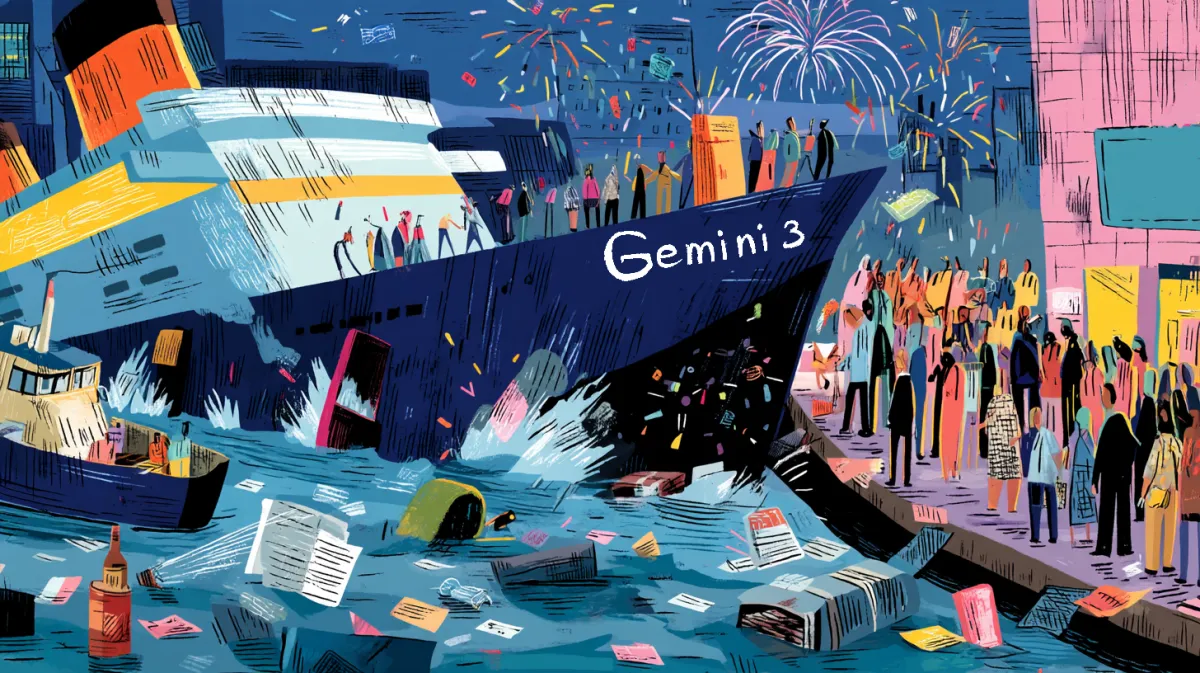
The most concrete response to the Gemini key incident was a small audit tool, not a think piece. In the Reddit post, keyguard is framed around one specific failure mode: projects where Gemini access is live on keys that were originally created for something else.
The linked GitHub repo splits that work into three commands:
keyguard audit: connect to live GCP projects and flag keys with Gemini accesskeyguard scan: search source files and git history for exposed credentialskeyguard ci: inspect GitHub Actions, CircleCI, and GitLab CI logs and variablesThat sits neatly beside Google's own restriction guidance, which says API keys should be limited by both client and callable API.
The second builder response was a thin gateway in front of model APIs. The Reddit post starts from a familiar mess, no clean per-user usage data, fuzzy cost tracking, and surprise rate-limit spikes once an app has more than one real user.
The linked Rust gateway repo adds the usual control-plane basics in one place:
For creative apps with many user-triggered generations, that kind of infra layer is more interesting than the model itself.
Individual-Bench4448's post is basically the architecture note a lot of teams write after hardcoding openai.chat.completions.create() in forty files. The four layers are clean enough to lift directly:
The post's claim was that a client moved 60 percent of calls after a pricing change with a config edit and two hours of testing. Even if the savings number is just one builder's anecdote, the structure is solid.
One more useful edge case came from an OpenClaw builder, who said ClawHub kept flagging a marketplace skill as suspicious because it called an external API and could run local scripts. Those were also the features the builder needed to connect users to local image and video generation backends.
That is a good reminder that control layers cut both ways. The same patterns that make key scans and gateway policies useful can also trip marketplace distribution when a tool needs outside network access and local execution.