Developers reported an active supply-chain attack affecting axios 1.14.1 and circulated IOC checks as the warning spread across security and AI circles. Fresh installs or unpinned deploys could resolve the compromised version, so pin and verify dependencies.
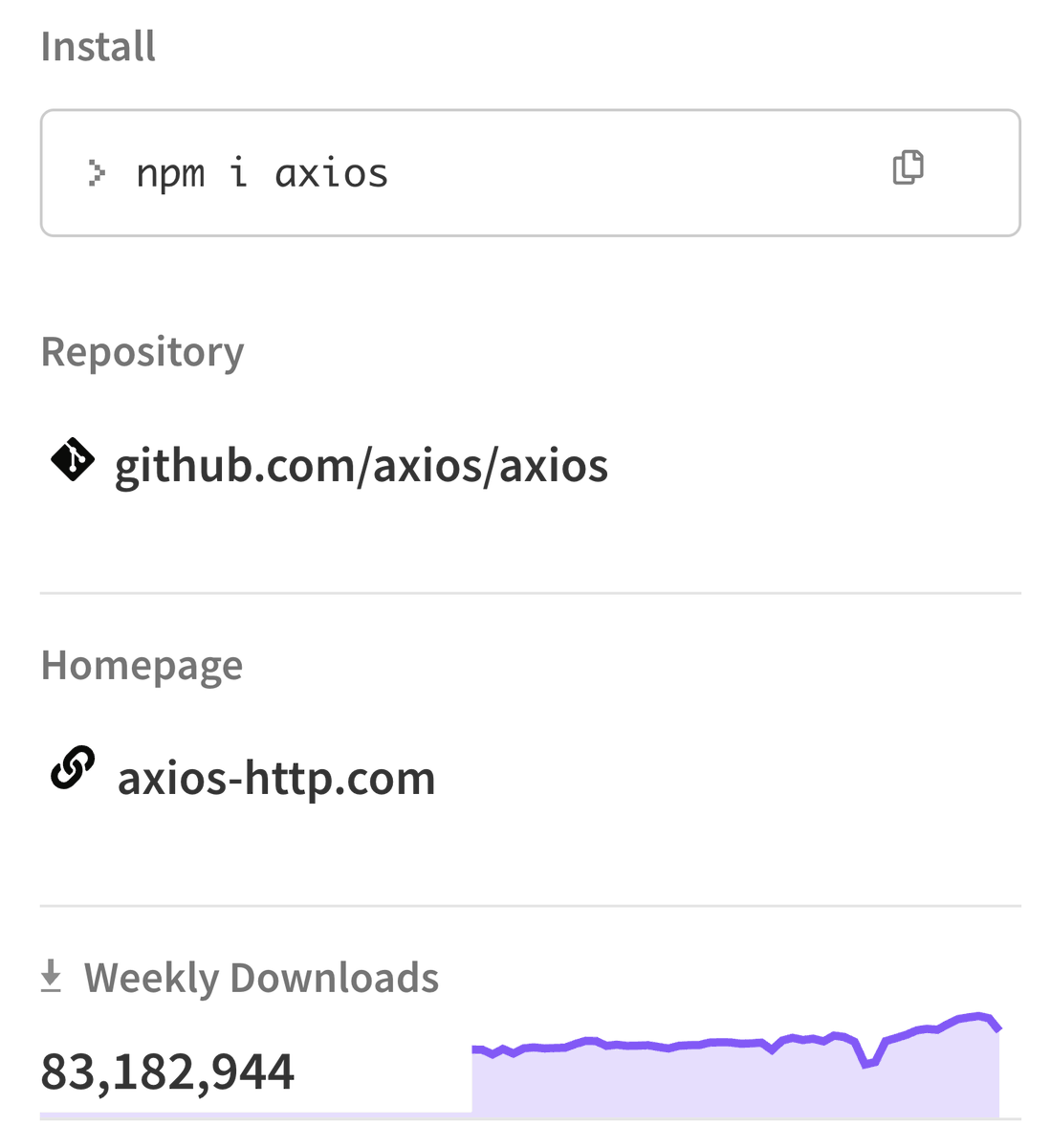
axios@1.14.1 was actively compromised, with Simon Willison urging teams to keep axios “pinned to a known safe version” in Simon Willison's warning.axios@1.14.1 and axios@0.30.4, while broader alerts said the latest axios build was pulling a malicious package during install feross retweet.sfrclak.com and a filesystem check that one responder said meant “you are pwned” if present, according to urgent IOC thread.The concrete breakage was not just “axios is bad.” The reported issue says axios@1.14.1 and axios@0.30.4 were compromised, and it links the problem to a malicious dependency drop plus possible maintainer-account compromise, adding that issue reports were being deleted. Separate warnings amplified that this was an active supply-chain attack on “one of npm's most depended-on packages,” with the latest build pulling malicious code at install time amplified alert.
That matters because npm users do not need to import axios directly to get hit. One widely shared warning said to “not npm install or deploy anything right now” because transitive resolution could still land the compromised version deployment warning. Karpathy described exactly that near miss: a project dependency from googleworkspace/cli was unpinned, and although his machine resolved to safe 1.13.5, he said an install “earlier today” would likely have pulled latest and “I'd be pwned,” according to Karpathy's example.
The strongest practitioner signal was timing. The urgent response thread targeted anyone who had run npm install, bun install, or an equivalent “in past couple hours,” then shared a quick triage path: blackhole the C2 domain, flush DNS, and check for a specific local artifact. The included terminal screenshot shows sfrclak.com mapped to localhost and a check for /Library/Caches/com.apple.act.mond; the post says that if the file exists, “shut down your machine immediately” terminal screenshot.
The fuller IOC summary linked from the follow-up post expands the scope beyond developer laptops. It says the malicious dependency was plain-crypto-js, that install-time payloads targeted macOS, Windows, and Linux, and that affected environments could include workstations, CI/CD systems, and production hosts if they installed the bad versions after the compromise window. That same summary also points to maintainer-account takeover indicators, including an npm email change, which is why the practical concern quickly shifted from a bad package release to a live ecosystem-wide supply-chain event.
holy shit axios is compromised right now
@npmjs @GHSecurityLab there is an active supply chain attack on axios@1.14.1 which pulls in a malicious package published today - plain-crypto-js@4.2.1 - someone took over a maintainer account for Axios
@npmjs @GHSecurityLab there is an active supply chain attack on axios@1.14.1 which pulls in a malicious package published today - plain-crypto-js@4.2.1 - someone took over a maintainer account for Axios
🚨 URGENT 🚨 if you have run npm install / bun install / equivalent in past couple hours run this - if IoC is found your device is cooked, shut it down and get it to infosec/IT folks asap
full IoCs here gist.github.com/joe-desimone/3…