Hermes Agent v0.7.0 adds memory plugins, credential pools, and Camofox browsing
Nous released Hermes Agent v0.7.0 with an extensible memory plugin system, rotating credential pools, Camofox browser support, and inline diff previews. The update pushes the framework closer to production use, so teams can test the new failure handling and interface split before adopting it.
TL;DR
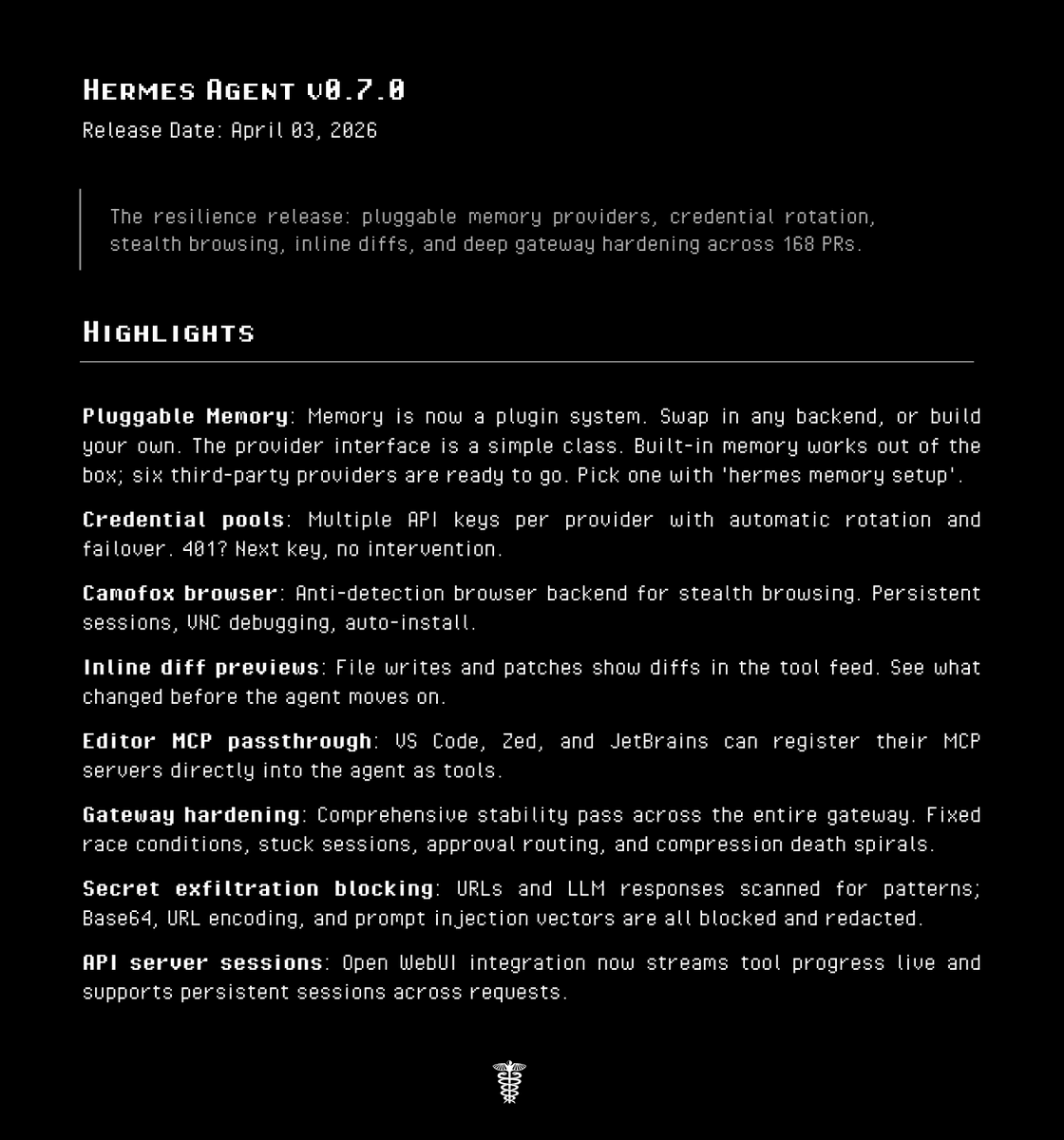
- Nous Research's launch thread framed Hermes Agent v0.7.0 as a memory and resilience release, and the official release notes add that it spans 168 PRs and 46 resolved issues.
- Teknium's breakdown says memory moved behind a provider interface, while the Memory Providers docs show seven external plugins alongside Hermes' built-in memory.
- Teknium's credential-pool post introduced same-provider key rotation, and the Credential Pools docs spell out the order: rotate inside the pool first, fall back to another provider only after the pool is exhausted.
- Teknium's Camofox post and the browser docs position Camofox as a local anti-detection backend with persistent sessions and VNC debugging.
- Teknium's diff-preview post covers the new inline patch view, while the release notes add less flashy but more consequential changes in API session persistence, editor-provided MCP servers, gateway race-condition fixes, and secret-exfiltration blocking.
You can jump straight into the full v0.7.0 release notes, skim the new memory provider list, compare it with the separate credential pool flow, and inspect the browser automation docs to see how Camofox sits next to Browserbase, Browser Use, and local Chrome.
Memory provider plugins
The core architectural change is boring in the best way. According to Teknium, Hermes is starting to push subsystems behind defined interfaces so the core code can stay smaller while third-party implementations expand around it.
The first subsystem to move is memory. The release notes describe an ABC-based plugin system with built-in memory still available by default, and the Memory Providers docs show the current external options:
- Honcho
- mem0
- OpenViking
- Hindsight by Vectorize
- RetainDB
- Byterover
- Holographic memory
That matters because Hermes now separates two kinds of persistence that often get blurred together. The docs say the built-in MEMORY.md and USER.md stay in place, while an external provider can add cross-session retrieval, background prefetch, and sync back from conversations into a dedicated memory backend.
Credential pools
Hermes now supports multiple credentials for the same provider, not just a single key plus a fallback vendor. In Teknium's example, that can mean a personal account and a corporate account cycling automatically for one provider.
The Credential Pools docs fill in the mechanics:
- pools are same-provider rotation, not cross-provider failover
- selection strategies include
round_robin,least_used,fill_first, andrandom - a transient 429 retries once on the same key
- a second 429 rotates to the next credential
- 401s trigger automatic rotation
- only after all pool keys are exhausted does Hermes switch to a fallback provider
The release notes also say pool state survives smart-routing and fallback transitions, which is the kind of detail you only add after seeing real traffic behave badly.
Camofox browser
Hermes already had browser tooling. v0.7.0 adds a new local backend aimed at stealthier automation.
The release notes call it a Camofox anti-detection browser backend with persistent sessions, VNC URL discovery for visual debugging, SSRF-bypass controls for local backends, and auto-install support through hermes tools. The browser automation docs add the implementation detail: Camofox is a self-hosted Node.js server wrapping Camoufox, a Firefox fork with fingerprint spoofing.
That puts Hermes in an odd but increasingly common place for open agent frameworks: not just calling models and tools, but shipping opinions about how to survive hostile websites.
Inline diffs, gateway fixes, and secret blocking
The CLI change is easy to grasp. File writes and patches now render inline diffs in the tool feed, and Teknium says the view is on by default but can be disabled.
The denser part of the release is everything grouped under hardening in the official notes. Nous says the gateway got fixes for race conditions, photo-media delivery, flood control, stuck sessions, approval routing, and what it calls compression death spirals. The same release also adds secret-pattern scanning across browser URLs and model responses, with blocking for exfiltration attempts that use URL encoding, base64, or prompt-injection tricks.
For teams running Hermes as more than a local toy, that cluster is probably the real headline. Memory plugins are the flashy part. Reliability work is what turns a fast-moving repo into something you can leave running.
API server sessions and editor MCP
The same v0.7.0 release notes tuck in two more upgrades that did not make the social posts. The API server now streams tool progress in real time and accepts X-Hermes-Session-Id headers so sessions can persist across requests in a shared SessionDB.
Nous also added client-provided MCP server support for editor integrations. In the release notes, that specifically means VS Code, Zed, and JetBrains can register their own MCP servers so Hermes can pick them up as additional tools.
That is a useful tell about where Hermes is heading. Teknium's repo-growth post said the project was already the third-fastest-growing GitHub repository that week, and the v0.7.0 changes read less like a feature dump than a framework trying to become a stable runtime for long-lived agents.